The FDA launched their up to date steerage on Cybersecurity in medical gadgets: High quality System Concerns and content material for Premarket submissions on the finish of June in 2025. On this steerage the FDA emphasizes the expectation that cybersecurity dangers and vulnerabilities be addressed in a menace mannequin. Cybersecurity procedures to help merchandise from preliminary design to finish of life should be carried out. Ample cybersecurity protections should be addressed within the design inputs throughout improvement and never “bolted on” after improvement is accomplished.
If you’re a developer or producer that’s or can be chargeable for a related medical machine, the cybersecurity course of is one thing it’s essential make investments effort in now.
There are a number of requirements similar to ANSI/AAMI SW96:2023 and IEC 81001-5-1: 2021 which might be widely known within the US and within the EU that element what actions and deliverables ought to be addressed relative to cybersecurity danger evaluation for medical machine software program. This quick article is concentrated on the best way to carry out the evaluation which is the core a part of the cybersecurity menace mannequin. The target for this text is to supply perception on conducting safety danger evaluation that’s impactful for the entire lifetime of a medical machine or medical machine software program.
Machine cybersecurity planning
From a pre-market perspective, the important thing parts to a safety evaluation are as follows:
 Determine 1 – Cybersecurity steps in danger evaluation
Determine 1 – Cybersecurity steps in danger evaluation
Along with planning for cybersecurity medical machine firms now have to implement a selected framework of their high quality system. To catch up to a degree of compliance some firms are making the error of addressing compliance by investing in a one-tool-does-all software program choice, however this will likely doubtless miss the true wants to handle cybersecurity in your group. The wholistic resolution is an software of a Safe Product Growth Framework that addressed the actions and duties all through the full product lifecycle (TPLC). Commissioning assets to develop and replace processes and SOP’s is required however the core of getting a stable course of is to determine an efficient and environment friendly danger evaluation technique. The danger evaluation technique is represented because the Safety Danger Evaluation within the evaluation part of determine 1.
Deal with Property in Safety Evaluation Desk
The Safety Danger Evaluation is used to determine potential safety danger controls and determine vulnerabilities. Two tables ought to be established, a Danger Evaluation desk that identifies and maintains the safety danger controls and the continuing vulnerabilities desk monitoring the present vulnerabilities. The 2 evaluation tables could be in separate tabs on a easy spreadsheet as they’ve filtering and sorting capabilities to permit for long run administration of the tables. The content material for the Danger Evaluation Desk is mirrored in Desk 1 addressing the Safety Controls.
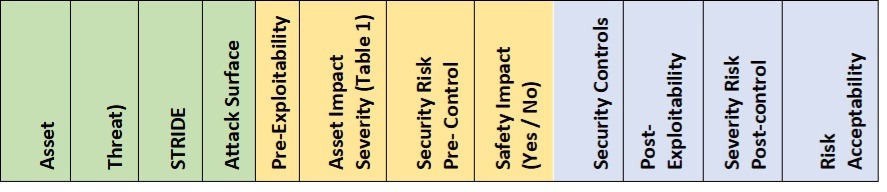
Desk 1 – Safety Danger Evaluation evaluation desk
The main target of the Safety Danger Evaluation ought to be the property outlined within the safety structure and the way threats could exploit vulnerabilities to compromise the property.
The property are parts which might be of worth to the consumer, affected person, consumer group and enterprise which might be related to safety. Property may typically embrace:
- Information dealt with and saved on the product (e.g., Logs, buyer or operational knowledge, configuration knowledge)
- Information of non-public nature (e.g., Protected Well being Info/PHI)
- Credential data (e.g., passwords, credentials, keys)
- Software program/firmware of the product
- Third occasion companies (e.g., cloud companies, open supply libraries, API’s).
The evaluation ought to embrace fairly sensible threats to every of the property. The STRIDE mannequin could be utilized to determine the potential menace in every evaluation row. The requirements STRIDE mannequin, and the specified safety property is offered in Desk 2 beneath.
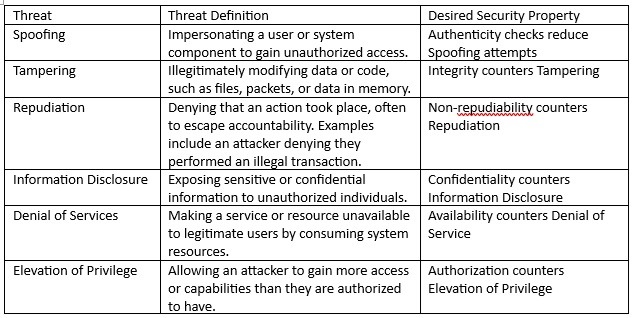
Desk 2 – Stride definitions
Vulnerability identification
Along with the Safety Danger Evaluation the separate ongoing vulnerabilities desk ought to be maintained, as talked about beforehand. This desk accommodates the identified vulnerabilities which were recognized within the machine. Vulnerabilities are flaws or weaknesses that could possibly be exploited by the potential threat-sources. Vulnerabilities could be recognized by way of:
- Figuring out vulnerabilities within the Safety Danger Evaluation
- cybersecurity penetration evaluation and testing of the product
- by way of static evaluation scanning of internally developed software program with SAST (Static Utility Safety Testing) software
- by way of a dynamic evaluation scanning with DAST (Dynamic Utility Safety Testing) software
- reviewing current catalogs just like the Widespread Vulnerabilities and Publicity Record, the Nationwide Vulnerability Database (NVD), the Nationwide Well being ISAC, and launch notes of SOUP/COTS.
- recognized by way of vulnerability scanning utilizing a SCA (Software program Composition Evaluation) software for OTS or open-source elements.
The analysis of identified vulnerabilities is critical previous to any product launch and maintained till the product is retired. As vulnerabilities are recognized and addressed, they might be faraway from the continuing vulnerabilities evaluation desk. Actions on the vulnerabilities are pushed by a severity dedication of the vulnerability and the CVSS rating. The CVSS scoring mannequin identifies six base objects in its matrix for every of the recognized vulnerabilities: Assault Vector (AV), Assault Complexity (AC), Privileges Required (PR), Person Interplay (UI), Scope (S) and Affect (CIA) measuring confidentiality, integrity and availability loss.
Decide influence of threats
In security danger evaluation we all know that danger is the mix of severity and chance of hurt (Danger = P x S). Nevertheless, for safety danger evaluation the FDA recommends contemplating the exploitability of a possible vulnerability versus the usage of chance of an assault occurring with success. Exploitability ought to be primarily based on how susceptible a system is to being compromised. The higher the safety controls the decrease the danger. The acceptability analysis of threats to property and vulnerabilities ought to be pushed by a desk matrix like to at least one in Desk 3, pushed by severity of hurt and exploitability.
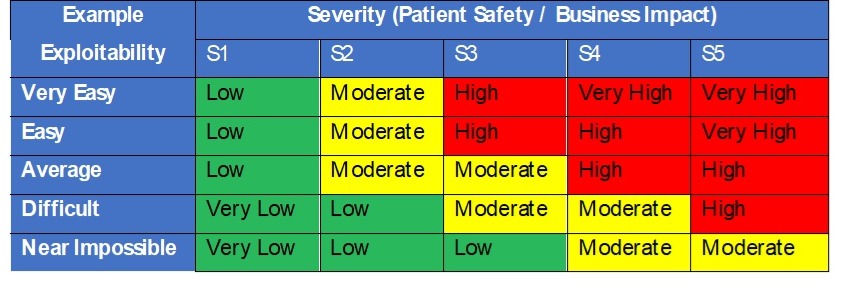
Desk 3 – Safety exploitability and severity resolution desk
Larger dangers would require documented danger controls within the Safety Danger Evaluation desk to cut back their exploitability and total danger. Danger controls ought to then drive necessities within the design and are subsequently verified as efficient throughout design verification.
Conclusion
The safety evaluation of dangers and vulnerabilities ought to be maintained in two tables, as one is required to determine and preserve the safety dangers and the opposite is an ongoing checklist of vulnerabilities that require periodic updates after launch. These two evaluation tables are to be up to date periodically and the continuing vulnerability checklist drive patch and buyer notification throughout product upkeep.
Whether or not your organization could also be simply beginning out or at a better level within the cybersecurity maturity spectrum of reaching a sturdy and environment friendly cybersecurity framework, a concentrate on the format and evaluation core practices as a precedence and can result in higher choices on instruments and enhancements within the course of effectivity and competency.
Photograph: Traitov, Getty Pictures

Bob Barrett, vice chairman of programs engineering at Full Spectrum, is an skilled engineering chief and workforce builder with a concentrate on outcomes. He has technical strengths gained from greater than 30 years in medical machine programs engineering, programs and software program validation, security danger evaluation, high quality administration and undertaking administration. Bob spent 15 years with Baxter’s drug supply division, the place he led the programs engineering group. Bob has the function of participant coach at Full Spectrum, main the programs engineering workforce, whereas offering his deep insights on to purchasers. Bob is a powerful believer in cadence pushed undertaking administration methods. His capacity to be hands-on or lead cross-functional groups accelerates consumer’s medical improvement packages from idea to market launch.
This put up seems by way of the MedCity Influencers program. Anybody can publish their perspective on enterprise and innovation in healthcare on MedCity Information by way of MedCity Influencers. Click on right here to learn how.